Diabolic Drive is a stealthy, wireless keystroke-injection tool that can send payloads over Wi-Fi while disguised as a regular 64 GB USB flash drive. Diabolic Drive is excellent for use in cybersecurity, particularly when red teaming, as it behaves like a typical flash drive until it is wirelessly instructed to deploy keystrokes.
Diabolic Drive adheres to the standard form factor of a "universal" USB drive, allowing it to be easily concealed with an inconspicuous flash-drive enclosure. When plugged in, anyone can interact with it like a normal flash drive, and it performs just like a genuine device, with average read speeds of up to 20 Mbps and write speeds of up to 10 Mbps. This behavior helps mask its wireless keystroke-injection features. Diabolic Drive is the first off-the-shelf product that combines all of these features into a single device. As such, it opens up untold social engineering attack possibilities.
Diabolic drive can be accessed remotely over Wi-Fi. Fire your payload remotely and precisely, or pre-program the drive to deliver keystrokes when plugged in.
By default, Diabolic Drive enters the "spectre" state, after it’s plugged in, rather than going "active" immediately. As long as it remains in that state, it appears only as a flash dive…right up until you deem it safe to expose the HID interface and begin injecting keystrokes, at which point you can initiate the attack remotely using a Wi-Fi connection to the onboard Web UI. Until then, the HID interface is completely dormant, with no unexpected behavior to detect and no abnormal logs generated.
For maximum stealthiness, Diabolic Drive allows you to spoof the identifying information it presents when connecting as a flash-storage device or as a human-interface device (HID).
While presenting itself as a storage device, Diabolic Drive can spoof its vendor ID (VID), product ID (PID), vendor info, product info, rev info, vendor string, product string, and serial number (SN), which makes it extremely challenging to distinguish from a regular flash drive. You can, for example, configure its vendor and product details to match any visible branding on its enclosure.
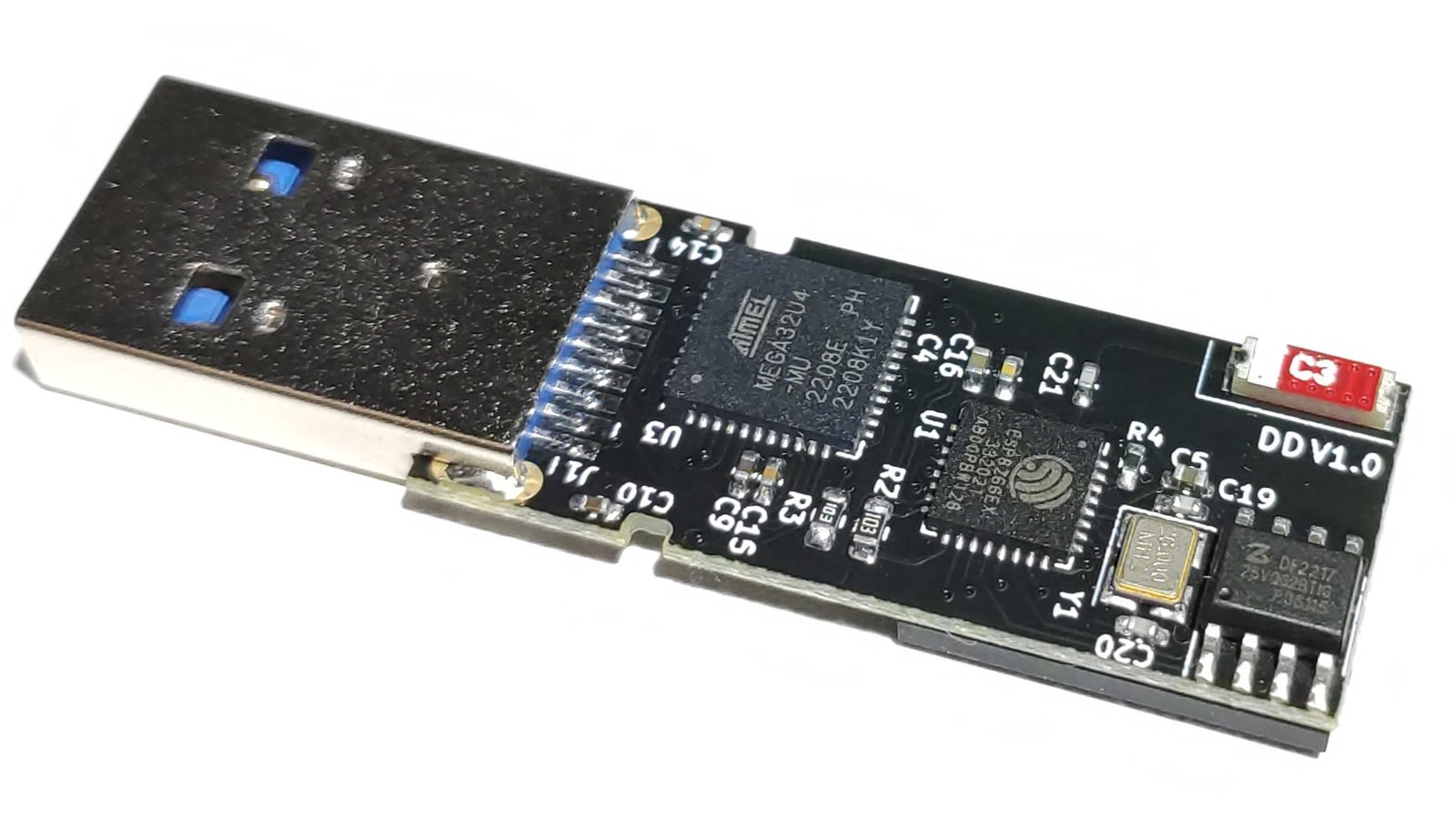
In order to inject keystrokes, Diabolic Drive must first present itself as an HID using its on-board ATmega32U4. When it does, it can spoof the VID and PID of a device—such as a keyboard—that was previously connected to the target. This prevents the appearance of a pop-up notification announcing the installation of a new HID. You can set and modify these identifiers on the fly using the onboard Web UI.
Diabolic Drive was designed for maximum capability and stealth, with an eye toward openness, flexibility, control, and future proofing. It contains the following components:
| Diabolic Drive | Rubber Ducky | O.MG CABLE Basic | USBNinja | |
|---|---|---|---|---|
| Form Factor | Flash drive | Flash drive | USB cable | USB cable |
| USB Type-C Availability | No | Yes | Available | Available |
| Flash Storage | Yes (64 GB) | No | No | No |
| OS Detection | Yes | Yes | No | No |
| Keystroke Reflection Exfiltration | Yes | Yes | No | No |
| Wireless Control | Wi-Fi | No | Wi-Fi | Bluetooth |
| Self-Destruct | No | No | Yes | No |
| Payload Over the Air (OTA) | Yes | No | Yes | No |
| OTA Firmware Upgradable | Yes | No | No | No |
| Different Enclosures Support | Yes | No | No | No |
| Price | $115 | $100 | $120 | $99 |
Upload Arduino Sketches by directly plugging your Diabolic Drive into your computer, as ATmega32U4 has native USB support through a built-in USB transceiver that handles the USB connection.
This unique feature gives you full control over Diabolic Drive’s ATmega32U4 through the device’s USB 3.0 pins. Diabolic Drive uses a modified version of the Arduino Leonardo bootloader but is compatible with the original version as well. You can reference the schematic in our GitHub repo to learn more.
You can find project information, programming instructions, design files, and a list of firmware options in our GitHub repository.
Produced by UNIT 72784 in Cairo, Egypt.
Sold and shipped by Crowd Supply.
stealthy wireless keystroke injection tool with 64 GB storage
Cybersecurity hardware company developing unique Red Teaming and Penetration Testing hardware devices.